Introduction
The idea of underwater communication has long been associated with secrecy, from military operations to deep-sea research. However, a new technological breakthrough is raising serious concerns—drones can now eavesdrop on underwater messages. This alarming advancement in surveillance technology threatens naval security, private maritime communications, and even scientific exploration.
In this article, we will explore how drones can intercept underwater signals, why this is a security risk, and what can be done to protect sensitive underwater communications.
How Do Drones Listen to Underwater Messages?
1. The Science Behind Underwater Communication
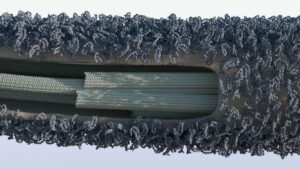
Underwater communication primarily relies on acoustic signals (sound waves) rather than traditional radio waves, as water absorbs electromagnetic signals. These acoustic signals, used in submarines, sonar systems, and marine research, were once considered difficult to intercept from the surface.
2. Advances in Drone Surveillance Technology
Recent technological advancements have made it possible for airborne and surface drones to pick up underwater acoustic signals. This is achieved through:
Hydrophone-equipped drones – These drones are fitted with advanced hydrophones (underwater microphones) that can detect and process acoustic waves traveling through water.
AI-Powered Signal Processing – Artificial intelligence helps these drones analyze and decode intercepted signals in real time.
Satellite-Connected Drones – Some drones can instantly transmit captured underwater messages to remote servers for further analysis.
3. Why Is This a Security Threat?
The ability of drones to eavesdrop on underwater messages presents several risks:
1. Military and Naval Security Breaches
Navies worldwide rely on secure acoustic communication for submarine operations, underwater drones (UUVs), and naval strategies. If adversaries can intercept these signals, it could compromise national security, leading to espionage and cyber warfare risks.
2. Threats to Commercial and Scientific Research
Oil rigs, deep-sea exploration teams, and marine researchers use underwater communication for critical operations. If unauthorized drones intercept these transmissions, intellectual property theft and data leaks could become serious concerns.
3. Maritime Trade and Subsea Cables at Risk
Submarine communication cables, which carry internet and financial data globally, could also be vulnerable to drone-based surveillance. Hackers or state-sponsored actors could exploit this technology to access sensitive global communications.
Can Underwater Messages Be Secured?
1. Encrypted Acoustic Communication
Just like internet data is encrypted, researchers are now working on encryption techniques for underwater acoustic signals to prevent unauthorized interception.
2. Anti-Drone Defense Systems
Navies and private industries are developing counter-drone technologies that can detect and neutralize suspicious drones hovering over sensitive waters.
3. Stealth Technology for Submarine Communication
New stealth-based acoustic communication methods, such as low-frequency encrypted signals, are being tested to reduce the chances of detection by airborne or surface drones.
4. Underwater Signal Masking
Some security experts suggest signal masking, where harmless noise is introduced to camouflage real acoustic messages, making it harder for drones to isolate and decode transmissions.
Conclusion
Drones capable of intercepting underwater messages mark a significant shift in modern surveillance and cyber-espionage. What was once considered secure underwater communication is now at risk, pushing military and private sectors to rethink security strategies.
While new encryption methods and anti-drone defenses are emerging, the race between security experts and surveillance technology developers is far from over.
As drone technology continues to evolve, so must the measures to protect sensitive underwater messages from being exposed to the wrong hands.
What do you think about this new security threat? Share your thoughts in the comments!




















+ There are no comments
Add yours